Information Security Experience That Works for You
Information Security Experience That Works for You
AsTech has been working with companies to secure their futures for over 20 years. Each person on our team of experts has completed quite a few laps around the sun, and brings that experience to the table to solve today’s security problems – and tomorrow’s.
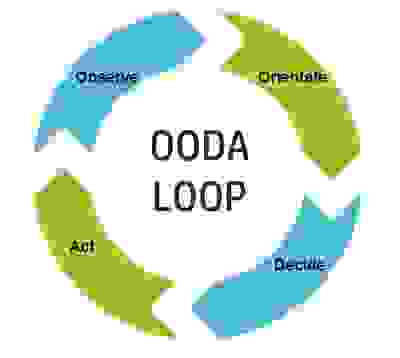
We understand that there is no ‘one-size-fits-all’ approach to many information assurance challenges, and know how to assess a situation, formulate a plan within constraints specific to that situation, and assist our clients in executing that plan. AsTech consultants adhere to the OODA Loop of continuous improvement, developed within the U.S. Air Force:
Our cybersecurity and information assurance experts evaluate current environments and maturity levels in areas affecting information security. We have deep expertise in many regulatory frameworks that drive a significant part of information security measures and reporting requirements. Our experts can evaluate assessments efforts completed by other third parties individually and in a concerted process, to identify gaps that may not be evident from looking at them as standalone and dissociated efforts. As we like to point out, it’s impossible to conclude the whole picture from just one piece of the puzzle.
Our team has expertise in evaluating whole security programs, incident response processes, secure software development programs, and other key aspects of information assurance that affect companies today.
With an understanding of where a company is compared to where it needs to be, developing the roadmap to get to a continuous improvement in the security posture is right in our wheelhouse. Our strategic and tactical recommendations come from a place of practical knowledge. From Incident Response capabilities to security organization to reporting to a Board of Directors, we have been there – we have seen what works . . . and what doesn’t work.
Many companies have the capabilities to implement the strategic recommendations that result from assessment and creation of the roadmap. AsTech works with them every step of the way to maximize outcomes, while transferring knowledge at each opportunity. For other companies, internal personnel resources may be fully deployed on existing projects so more hands on project management assistance is needed. AsTech can provide this expertise to execute the roadmap to achieve results. Either way, we help get the job done.
For more information, contact us.
If we can help achieve information security success for your company, we will.
700 Larkspur Landing Circle Ste 199 415-786-7857
Larkspur, CA 94939
Copyright © 2021 AsTech Consulting - All Rights Reserved.
Powered by GoDaddy